What is network access control list?
A network access control list (ACL) used to control network level security. It controls traffic to or from a subnet level, by configuring inbound and outbound traffic rules.

Important points about Network ACL
- By default, VPC comes with a modifiable default network ACL and it allows all inbound and outbound IPv4/IP6 traffic.
- You can create a custom network ACL and associate it with a subnet. By default, each custom network ACL denies all inbound and outbound traffic, you need to add the rules.
- Each subnet must be associated with a network ACL. By default subnet is automatically associated with the default network ACL. You can explicitly change association between subnet and Network ACL.
- Network ACL is stateless: It means changes applied to an incoming rule will not be automatically applied to the outgoing rule. you need to explicitly allow the outgoing rule.
- Network ACL process rules in order, rule with the lower number gets processed first, when deciding whether to allow traffic. The highest number that you can use for a rule is 32766.
- AWS recommend that you start by creating rules in increments (for example, increments of 10 or 100) so that you can insert new rules where you need to later on.
Components of Network ACL rules
Below image is an example default network ACL for a VPC that supports IPv4 and IPv6. We can also add rules with an asterisk that ensures that a packet is denied if no other numbered rules matched.
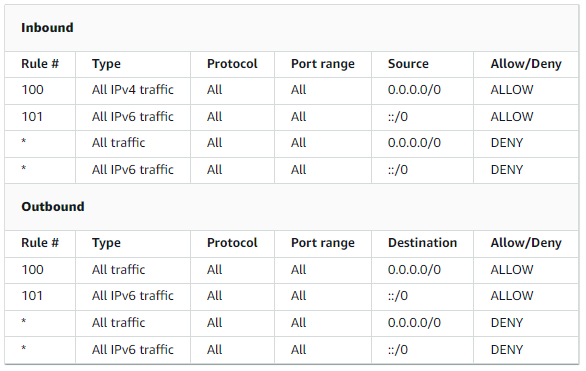
- Rule number: Rules are evaluated starting with the lowest numbered rule. As soon as a rule matches traffic, it gets executed regardless of any higher-numbered rule that might contradict it.
- Type: The type of traffic, For example TCP, UDP, ICMP, SSH. You can also select a custom protocol rule.
- Protocol: You can specify any protocol that has a standard protocol number. Read more form here: Protocol Numbers.
- Port range: Add the port or port range for the traffic ( For example, 80 for HTTP traffic or port range like 5000–7000)
- Source (Inbound rules only) : The source IP address (Single IP or CIDR range).
- Destination (Outbound rules only): The destination IP address (Single IP or CIDR range).
- Allow/Deny: Define whether to allow or deny traffic.
What is network access control list
