What is AWS Security Groups?
Amazon Security group acts like a virtual firewall for your EC2 instances, They control both inbound and outbound traffic. When you launch an instance you need to link it with a VPC, Subnet, and at least one security group.
Important points about security group
- Security groups act at the instance level, not the subnet level.
- You can have any number of EC2 instances within a security group.
- You can assign up to five security groups to the instance.
- Each instance in a VPC subnet can be assigned to a different set of security groups.
- When you create a security group, By default all inbound traffic is blocked, and all out traffic is allowed.
- You can specify allow rules, but not deny rules.
- Security group rules allow you to filter traffic based on protocols and port numbers.
- You cannot block specific IP address using a security group.
- Security groups are stateful — if you create an inbound rule allowing traffic in, traffic for that request is automatically allowed to flow out, regardless of outbound rules.
Default Security Group of VPC
Every VPC automatically comes with a default security group. If you don’t specify any security group when you launch the EC2 instance, your instance will be associated with the default security group.
In the default security group allows communication between all resources within the security group, allows all
outbound traffic, and denies all other traffic.
You can change the rules for the default security group, but you can’t delete a default security group.
Security group rules
There are two types of security group rules:
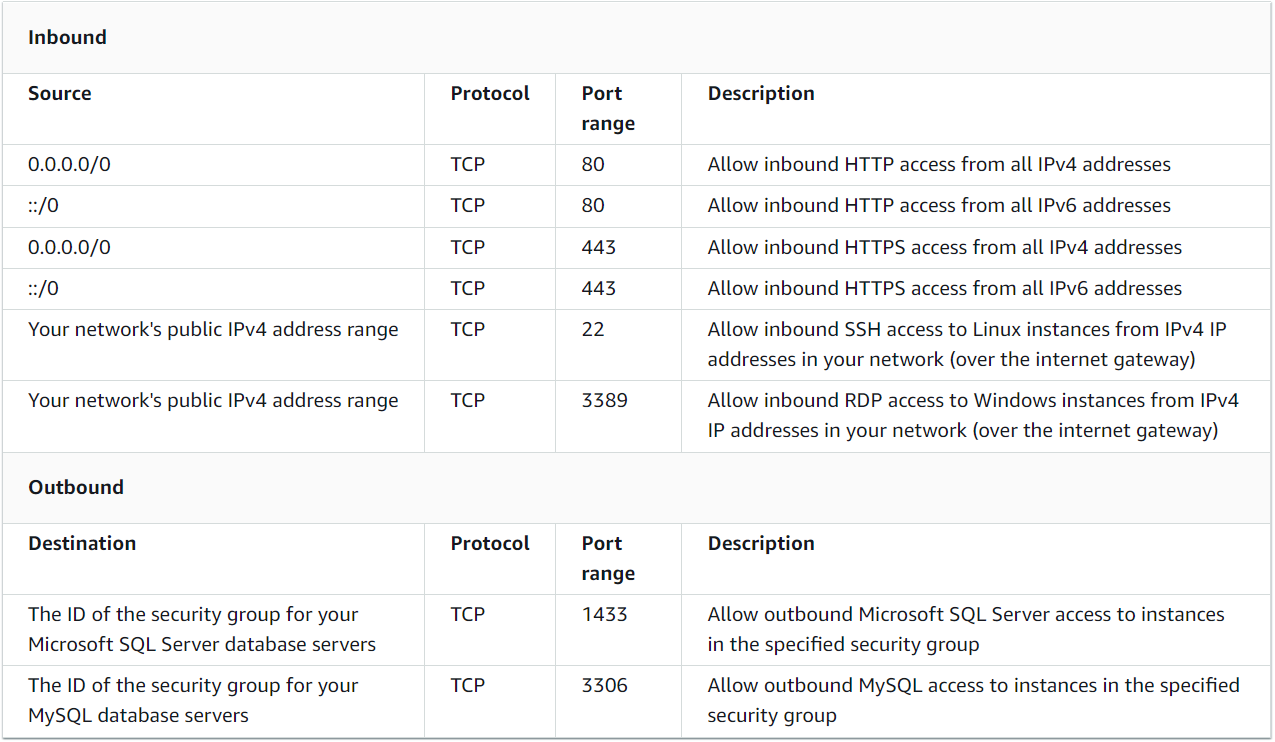
Inbound: Inbound rules control the incoming traffic to reach the instances that are associated with the security group.
Outbound: Outbound rules control the traffic to leave the instances that are associated with the security group.
For each inbound and outbound rule, you can add, update, or remove rules that take effect immediately in all instances associated with the security group. Each rule consists of the following key elements:
Name: The name for the security group (for example: webserver-security-group, database-security-group).
Protocol: The network protocols to allow (for example: TCP, UDP, ICMP, etc.).
Port range: A specific port or the range of ports to allow traffic on (for example: 80, 22, 7000-8000, etc.).
Source or destination: The source (inbound rules) or destination (outbound rules) for the traffic that can specify by an IP, IP range, or other security groups.
For example, the web servers can receive HTTP and HTTPS traffic from all IPv4 and IPv6 addresses, and can send SQL or MySQL traffic to a database server.